Project leader:
Project members:
Start date: 1. October 2018
End date: 30. September 2021
Funding source: Deutscher Akademischer Austauschdienst (DAAD)
Project Partner Website: Refinio GmbH

Abstract
The patient-centred healthcare ecosystem (PHE) is a future digital healthcare model where all healthcare stakeholders will eventually transition from an isolated approach to a collaborative approach around the patient. Among other benefits, the PHE will enable individuals to take control of their health information in a confidential and secure environment. Currently evolving PHEs either use a centralized database or blockchain technology for storing medical records.
On the one hand, healthcare industries that store data in a centralized database experience more data breaches than any other sector, as revealed in the latest report by the Office of the Australian Information Commissioner on data breaches. Moreover, the Protenus Breach Barometer in the US reported 369 health data breaches in the third quarter of 2018, affecting 8 million patients. On the other hand, the immutable nature of data storage in blockchain makes it impossible for users to erase their stored information, which goes in contrary to the European regulation on data protection.
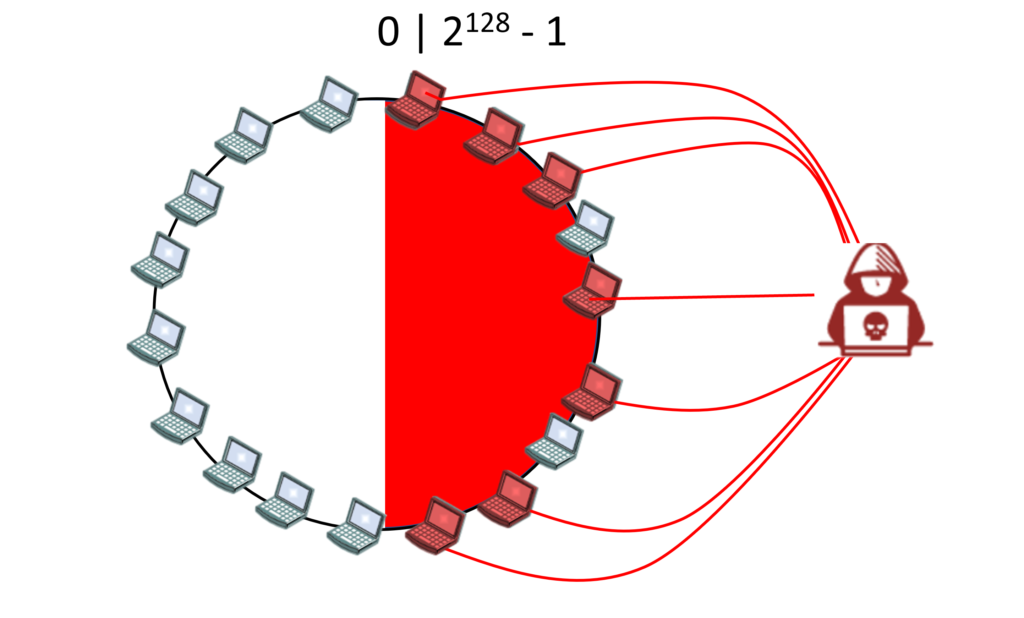
The OnePatient PHE by Refinio ONE (a German-based health technology startup) is based on peer-to-peer technology; an alternative to centralized database and blockchain technology. Although blockchain also uses peer-to-peer technology, the data is inherently shared publicly, and in case the blockchain encryption gets broken, all the data becomes public. In contrast, when the OnePatient PHE encryption gets broken, only one user is affected at a time. However, storing medical records in peer-to-peer technology still requires research in terms of security and education and awareness to users about data security and privacy.
In our work, we aim to i) investigate the possible and inherent security and privacy issues for future PHEs like OnePatient, ii) design security models such as Firewall, Trust Reputation System, etc. to provide additional security, and iii) finally evaluate the effectiveness of our security models.
Related Publications
- , , , , :
Online at Will: A Novel Protocol for Mutual Authentication in Peer-to-Peer Networks for Patient-Centered Health Care Information Systems
In: 54th Hawaii International Conference on Systems Sciences (HICSS-54) 2021
DOI: 10.24251/hicss.2021.463
URL: https://scholarspace.manoa.hawaii.edu/handle/10125/71079
BibTeX: Download - , , , , , :
Security Engineering of Patient-Centered Health Care Information Systems in Peer-to-Peer Environments: Systematic Review
In: Journal of Medical Internet Research 23 (2021), p. e24460
ISSN: 1438-8871
DOI: 10.2196/24460
URL: https://www.jmir.org/2021/11/e24460
BibTeX: Download